Blog
From Null to Known: Crossover Cables, Cheat Engine, and a Plot Twist
2026-02-23

I did not start in cybersecurity with a polished roadmap.
I started with two old desktop PCs, one crossover cable, and a lot of trial and error.
Phase 1: Two PCs, dial-up, and chaos
In primary school, I tried to run a tiny two-PC internet cafe at home.
Friends paid a small fee to play online games. Dial-up made the usual alien noises in the background.

I learned from forums like pc-experts, then tested everything myself.
I also fried a desktop while overclocking and swapping parts.
The PC died. The curiosity stayed.
Phase 2: Linux and the terminal pull
Then I found Linux.
I did not understand much at first, but I was hooked by the terminal and how fast experts moved with it.
So I focused on fundamentals:
- Building and fixing PCs
- Installing and reinstalling operating systems
- Learning how systems behave when they break
Phase 3: My first security practice came from game cheating
This part is honest.
My first security-related experiments were game memory edits with Cheat Engine and hex tweaks.
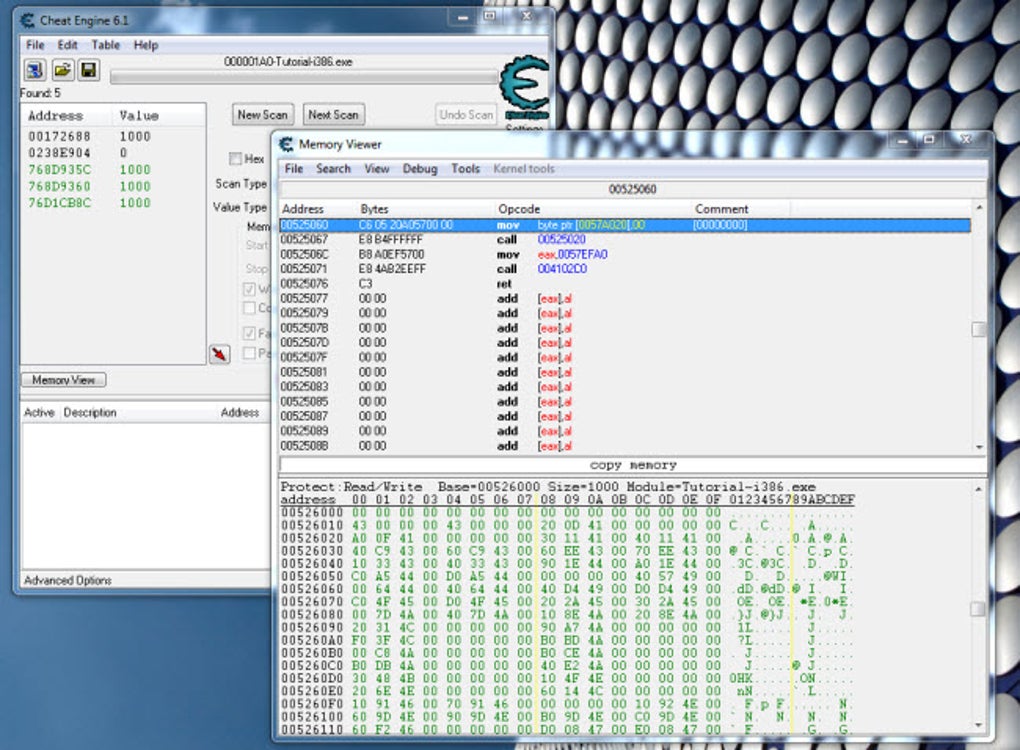
At the time, I did not see it as security work. I later learned it overlaps with reverse engineering thinking.
Phase 4: University and first IT job
I studied Electronics and Communications Engineering, not computer science.
Still, I kept joining Linux workshops and practical tech sessions.
That preparation helped me land my first role as a Desktop Support Engineer.
Phase 5: IT operations, networking, and CCNA
Support work taught me real production constraints.
I learned from incidents, patch cycles, user issues, and systems that fail in messy ways.
I studied networking seriously, completed CCNA, and built stronger foundations.
Phase 6: The pentest moment
At PropertyGuru, I shadowed an external pentester while handling sysadmin and network work.

Seeing attack paths chained from small weaknesses changed how I viewed security.
It was methodical and practical, not movie hacking.
Phase 7: DevOps detour, then return to security
As responsibilities grew, I focused on cloud, platform, and DevOps delivery.
Security moved to the background for a while.
Now I am returning with more structure and better goals through the HTB CJCA path.
If you want the timeline view, check my projects.
Why this blog exists
This is my working portfolio.
You will see:
- Home lab builds
- Sanitized HTB and THM notes
- Practical security projects
- What worked, what failed, and what I changed
If you are switching into cybersecurity, this journey will show the real process, not only polished wins.